
Security Key safeguards Twitter Account like never before
Complex security protocols can be difficult to implement for any enterprise. That does not mean that it is not necessary. The Twitter Story Back in

Complex security protocols can be difficult to implement for any enterprise. That does not mean that it is not necessary. The Twitter Story Back in

The US Federal Trade Commission (FTC) reported in 2020 that Americans were swindled out of over $1.9 billion as a result of fraudulent transactions in

Cybersecurity is more important than ever right NOW. Thanks to the use of Security Keys No emails leaked from the 2020 election campaigns!! https://www.cnbc.com/2020/12/23/physical-security-keys-protected-2016-election-campaigns-against-leaks.html?&qsearchterm=security%20key Find

The FIDO (Fast Identity Online) standard strengthens the security of online authentication systems for mobile devices and web applications. Their aim is to replace the

It’s a known fact that to log in to Windows it is necessary to use a username and a password. Or without a password, if

Passwordless authentication is a verification process that determines if someone is who they say they are without requiring the person to manually enter a string.

According to a Nationwide survey, phishing ranks among the most common cyber threats businesses face. Second only to computer virus attacks. Phishing follows a familiar

What is a Phishing Attack? Phishing is an online scam. Criminals create fraudulent emails that appear legitimate and send them out unsuspecting victims. You may
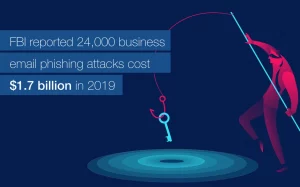
Phishing and cyber-attacks cost more than you think or can afford. In 2019 IC3 the FBI’s Internet Complaint Center received just under half a million

Since mid-2017 not one of Google’s over 85,000 employees has been successfully phished on their Google work accounts. All because that’s when Google enforced 2-step-verification




Scan QR code to download GoTrust ID mobile APPs






Scan QR Code to Download Application for Mobile Device

